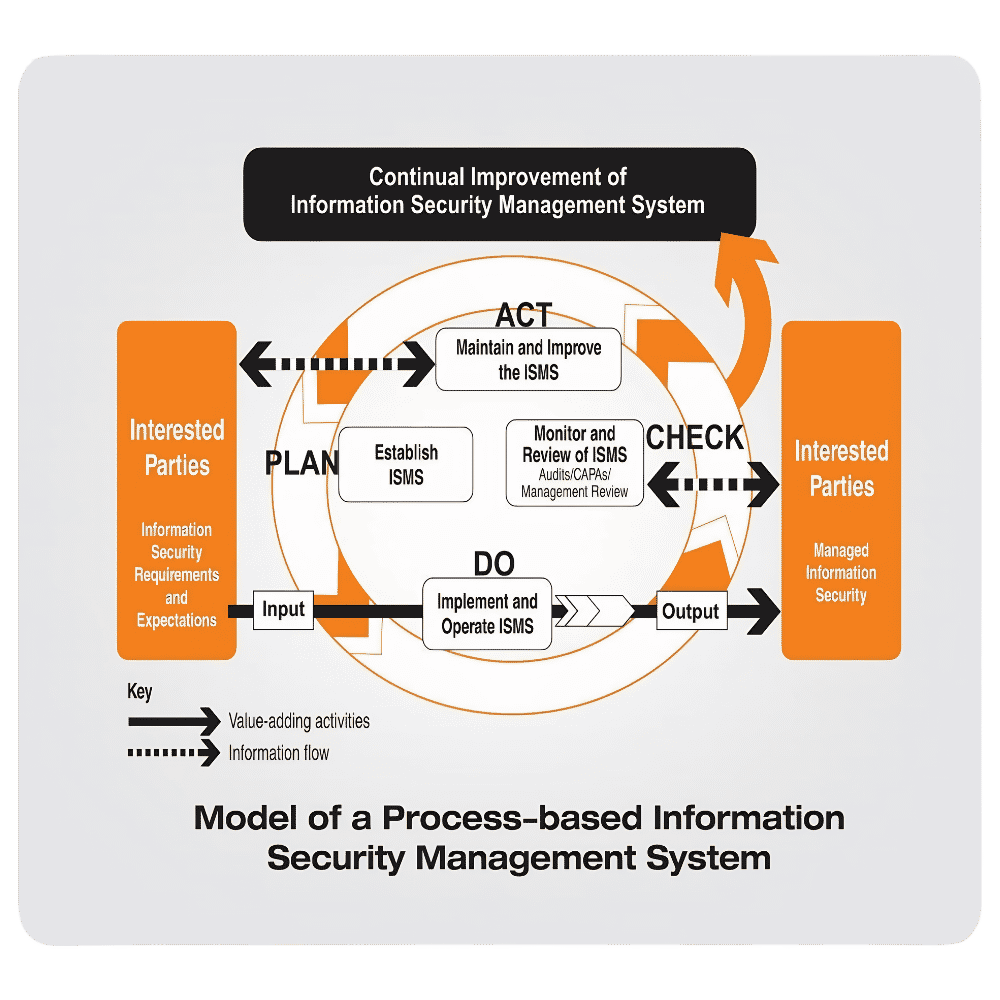
ISO/IEC 27001 ISMS
End-to-end Information Security Management System implementation aligned with ISO 27001:2022.
- Scope definition and Statement of Applicability (SOA)
- Risk-based asset assessment and treatment
- Annex A control design and operationalization
- Internal audit, management review, and Stage 1/2 audit support